When you first stumble upon a powerful developer tool, there’s usually a mix of excitement and caution. That’s exactly how many people feel when they discover dnspy.org. Is it safe? Is it legal? And more importantly, what can it actually do?
In a world dominated by compiled applications and proprietary software, tools that let you peek under the hood feel almost magical. dnspy.org is widely associated with dnSpy, a well-known open-source .NET decompiler and debugger that has built a loyal following among developers, cybersecurity professionals, and reverse engineers.
If you’re here, you’re probably curious—whether for legitimate debugging, academic research, malware analysis, or pure technical exploration. This guide will walk you through everything you need to know about dnspy.org, from functionality and security concerns to real-world use cases and best practices.

What Is dnspy.org?
At its core, dnspy.org is commonly referenced as a website associated with dnSpy, a popular open-source tool for decompiling and debugging .NET assemblies. dnSpy itself is not a typical consumer application—it’s a technical utility used primarily by developers and security analysts.
dnSpy allows users to:
- Decompile .NET assemblies into readable C# or VB.NET code
- Edit Intermediate Language (IL) code
- Debug managed applications
- Analyze third-party binaries
When people search for <strong>dnspy.org</strong>, they’re usually looking for downloads, documentation, or clarification about whether the source is trustworthy.
Why It Matters
In .NET development, applications are compiled into Intermediate Language (IL) and then executed by the Common Language Runtime (CLR). While this provides portability and efficiency, it also means that reverse engineering is technically feasible. Tools like dnSpy make this process accessible and structured.
However, accessibility brings responsibility—which we’ll discuss shortly.
Understanding dnSpy and Its Core Features
1. .NET Decompilation
One of the primary reasons people visit dnspy.org is for dnSpy’s powerful decompiler.
Decompilation transforms compiled assemblies (DLL or EXE files) back into high-level source code such as:
- C#
- Visual Basic .NET
This is particularly useful for:
- Debugging legacy applications
- Recovering lost source code
- Security research
- Learning from third-party implementations
The accuracy of dnSpy’s decompilation engine is one reason it became so widely adopted in developer circles.
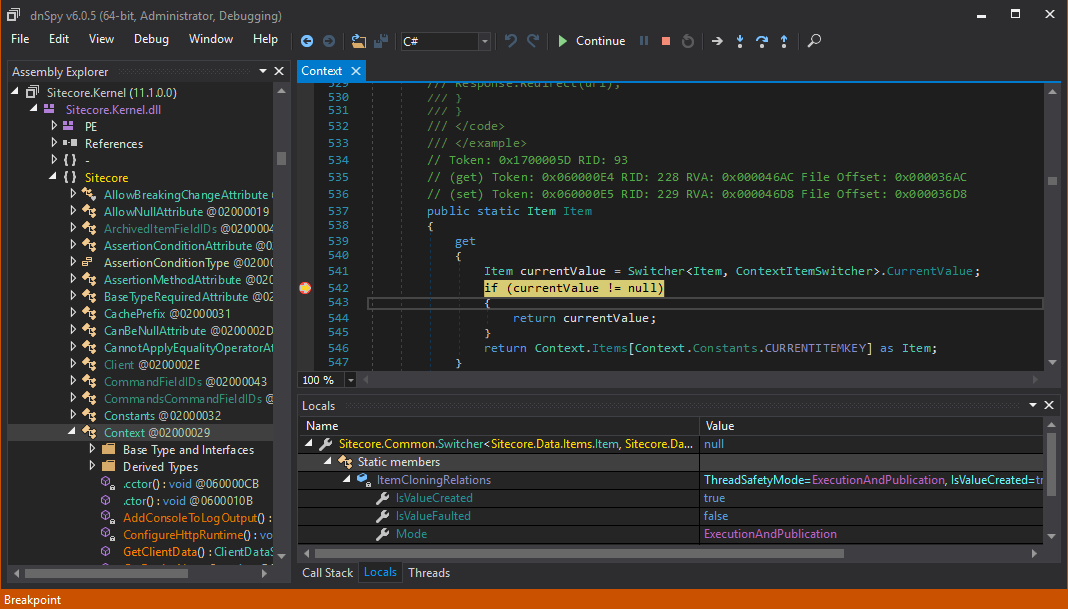
2. Integrated Debugger
Unlike many standalone decompilers, dnSpy includes a built-in debugger.
This enables users to:
- Set breakpoints
- Step through code execution
- Inspect variables and memory
- Analyze runtime behavior
For cybersecurity analysts, this is invaluable when investigating suspicious binaries or malware samples.
3. Assembly Editing
dnSpy also allows users to edit and recompile assemblies. This capability is powerful—and potentially dangerous if misused.
Developers may use this for:
- Patching test builds
- Quick fixes in internal tools
- Learning and experimentation
However, modifying proprietary software without authorization can violate licensing agreements.
4. IL Editing
Advanced users can work directly with IL (Intermediate Language). This provides granular control over program behavior but requires deep knowledge of .NET internals.
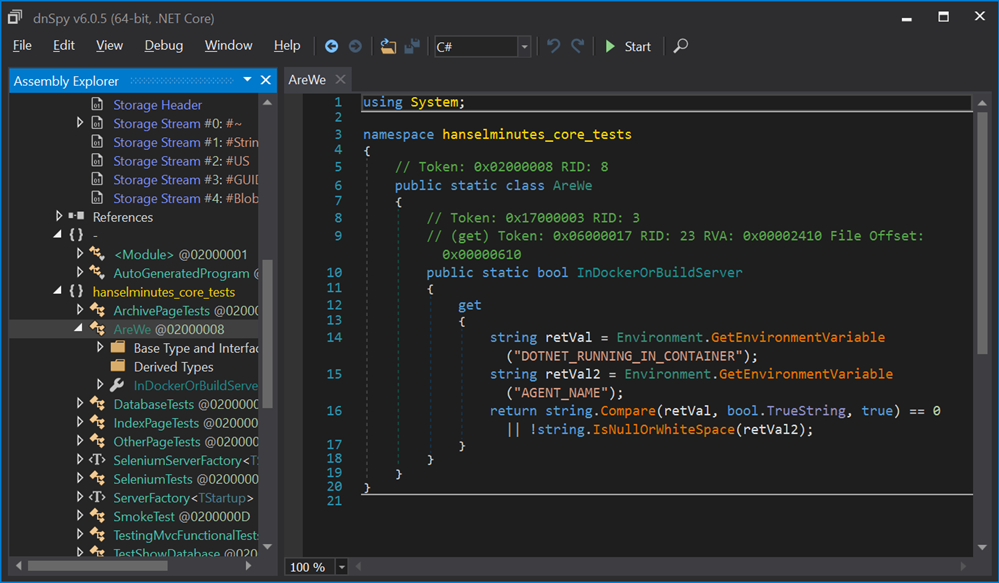
How dnSpy Works: Behind the Scenes
To understand dnspy.org properly, you need to grasp how .NET applications function.
When you compile a .NET project:
- Source code (C#, VB.NET) is compiled into IL.
- IL is stored in assemblies (DLL/EXE).
- The CLR executes IL at runtime.
Because IL retains structural metadata, decompilers can reconstruct readable source code. dnSpy parses assembly metadata and translates IL back into high-level language constructs.
The Technical Workflow
- Load assembly file
- Parse metadata tables
- Interpret IL instructions
- Map instructions to language syntax
- Render structured source code
In practice, decompilation isn’t perfect. Variable names may be altered, comments are lost, and some optimizations complicate reconstruction. Still, dnSpy often produces surprisingly clean results.
Is dnspy.org Safe and Legitimate?
This is the question that drives most search traffic.
Security Considerations
The safety of dnspy.org depends largely on:
- Whether the website hosts official builds
- Whether the files are digitally signed
- Whether downloads are verified via checksums
Because dnSpy is open-source, official releases are typically distributed via platforms like GitHub. Always cross-check file hashes before installing.
Red Flags to Watch For
- Unexpected browser redirects
- Forced installer downloads
- Bundled adware
- Modified executables
If something feels off, it probably is. Always verify authenticity before running executable files.
Legal and Ethical Considerations
This is where nuance matters.
Using dnSpy for:
- Debugging your own applications → Legal
- Academic research → Typically legal
- Malware analysis → Legal in controlled environments
- Cracking paid software → Illegal
Reverse engineering laws vary by country. In the U.S., for example, the Digital Millennium Copyright Act (DMCA) contains provisions around circumvention of protection mechanisms.
Ethical use matters just as much as legal boundaries. Just because you can decompile something doesn’t mean you should.
Installing and Using dnSpy Safely
If you’re determined to explore dnspy.org-related tools, follow best practices:
Step-by-Step Safety Checklist
- Download only from verified repositories
- Check SHA256 hash values
- Scan files with updated antivirus software
- Use a virtual machine for testing
- Avoid modifying production software
For cybersecurity researchers, isolating analysis environments is standard practice. Tools like sandboxed VMs reduce risk dramatically.
Real-World Use Cases of dnspy.org
Let’s move beyond theory.
1. Recovering Lost Source Code
A small development team once lost its Git repository due to server corruption. Their only backup was a compiled build. Using dnSpy, they recovered enough C# logic to rebuild the project.
2. Malware Analysis
Security researchers often use dnSpy to inspect suspicious .NET malware. By stepping through execution and examining strings, they can uncover:
- Command-and-control servers
- Obfuscated payload logic
- Encryption routines
3. Learning Tool for Developers
Many junior developers use dnSpy to understand how popular open-source projects structure their assemblies. It’s like opening the hood of a car to see how the engine works.
Comparison With Other .NET Decompilers
| Feature | dnSpy | ILSpy | dotPeek |
|---|---|---|---|
| Decompilation Accuracy | High | High | High |
| Built-in Debugger | Yes | No | Limited |
| Assembly Editing | Yes | No | No |
| Open Source | Yes | Yes | No |
| User Interface | Advanced | Simple | Polished |
dnSpy stands out because of its debugger integration and editing capability.
Developer Background and Community Insights
Unlike commercial tools, dnSpy originated as an open-source initiative. Over time, it gained traction among:
- Independent developers
- Security professionals
- Reverse engineers
- Academic researchers
Although development activity fluctuated, the community continues to maintain forks and updates.
Community Strength
The open-source ecosystem ensures:
- Transparency
- Peer review
- Faster bug detection
- Collective improvement
In many ways, dnSpy’s popularity isn’t driven by marketing—it’s driven by utility.
FAQ
What is dnspy.org mainly used for?
dnspy.org is typically associated with dnSpy downloads and documentation. dnSpy itself is used for decompiling, debugging, and analyzing .NET assemblies.
Is dnSpy legal to use?
Yes, when used for legitimate purposes such as debugging your own code or academic research. Illegal activities like software cracking are prohibited.
Can dnSpy recover lost source code?
In many cases, yes. It can reconstruct readable C# code from compiled .NET assemblies.
Is dnspy.org an official website?
Users should verify official sources carefully. Always confirm authenticity before downloading.
Does dnSpy work on .NET Core?
Support varies depending on build versions. Newer forks aim to maintain compatibility with modern .NET frameworks.
Can dnSpy edit compiled applications?
Yes. It can modify IL and recompile assemblies—but this should be done ethically and legally.
Is dnSpy safe from malware?
The tool itself is safe when downloaded from verified sources. Always scan downloads before execution.
What alternatives exist?
ILSpy and dotPeek are common alternatives, though feature sets differ.
Conclusion
In a digital ecosystem where compiled code often feels opaque, dnspy.org represents curiosity, capability, and caution all at once. dnSpy is undeniably powerful—able to decompile, debug, and modify .NET assemblies with impressive accuracy.
However, power requires responsibility. Used ethically, dnSpy becomes a learning instrument, a debugging assistant, and a research ally. Misused, it crosses legal and moral boundaries.
If you approach dnspy.org with technical discipline and ethical clarity, it can be one of the most insightful tools in the .NET ecosystem.